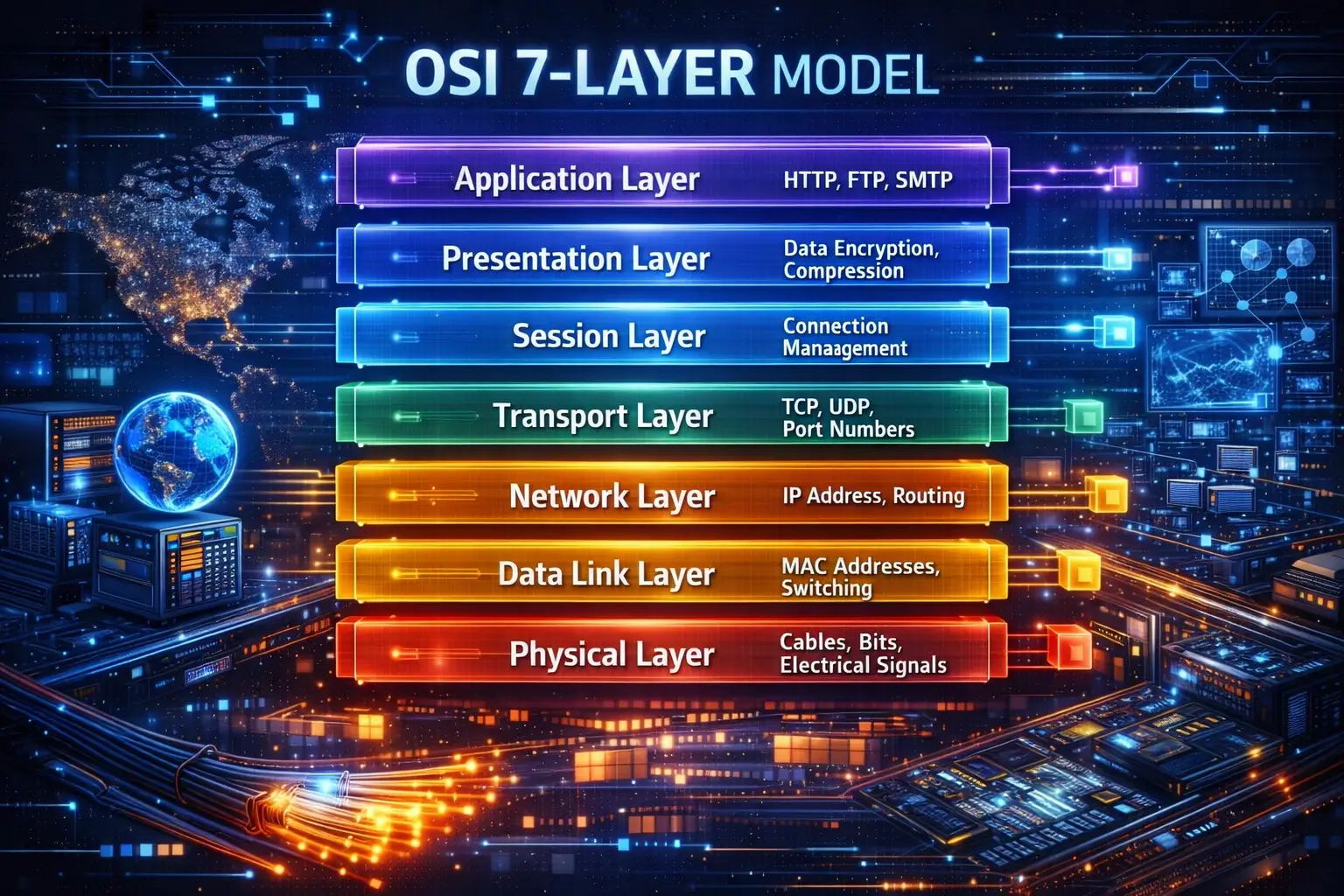
In cloud-native systems—where applications run inside containers, behind proxies, across virtual networks—the OSI model becomes less about theory and more about structured thinking under pressure.
Let’s walk through the OSI model from Layer 7 down to Layer 1, exactly how problems usually present themselves in production.
Layer 7: Application – Where Problems Are Felt First
What it looks like today
- HTTP / HTTPS
- REST and GraphQL APIs
- gRPC
- DNS
- SMTP, FTP
Why this layer matters
Layer 7 is where humans interact with the network. Error pages, API failures, slow responses—this is where incidents are reported, dashboards light up, and SLAs are breached.
Modern scenarios
- API gateways enforce authentication, rate limiting, and request validation.
- Web Application Firewalls (WAFs) inspect payloads for SQL injection or XSS without touching lower layers.
- Microservices communicate via HTTP or gRPC, often hiding network complexity behind service meshes.
Troubleshooting insight
A 500 Internal Server Error might not be an application bug at all. It could be:
- A downstream service timing out (Layer 4)
- A routing issue between subnets (Layer 3)
- Packet loss between nodes (Layer 2)
Layer 7 shows symptoms—not causes.
Layer 6: Presentation – Encryption, Encoding, and Trust
What it looks like today
- TLS/SSL encryption
- Certificate chains
- Compression
- Data serialization (JSON, XML, Protobuf)
Why this layer matters
This is where data becomes readable, secure, and interoperable. Modern security expectations live here.
Modern scenarios
- TLS termination at reverse proxies or load balancers to offload CPU work.
- Mutual TLS (mTLS) in zero-trust architectures to authenticate services, not just users.
- Certificate mismanagement causing total outages even when servers are healthy.
Performance and security trade-offs
Encryption adds overhead. Knowing where TLS is applied helps optimize latency without weakening compliance or security posture.
Layer 5: Session – Continuity Across Time
What it looks like today
- Login sessions
- Session cookies
- Persistent connections
- TLS session resumption
Why this layer matters
Layer 5 keeps interactions coherent. Without it, every request would feel like the first one.
Modern scenarios
- Load balancers using session affinity for stateful legacy applications.
- Kubernetes rolling updates accidentally terminating sessions mid-request.
- OAuth tokens maintaining identity across distributed services.
Security insight
Session hijacking exploits weaknesses here. Poor expiration policies or token reuse can bypass authentication even when Layer 7 logic is correct.
Layer 4: Transport – Reliability, Speed, and Scale
What it looks like today
- TCP and UDP
- Ports
- Connection states
- Load balancers (L4)
Why this layer matters
Layer 4 determines how data moves—reliably or fast, ordered or unordered.
Modern scenarios
- TCP dominates APIs and web traffic; UDP powers DNS, streaming, and real-time communication.
- Cloud load balancers distribute traffic at Layer 4 without understanding HTTP.
- Container-heavy environments burn through ephemeral ports faster than expected.
Troubleshooting insight
If a service works sometimes but fails under load, Layer 4 may be the culprit:
- Port exhaustion
- SYN floods
- TCP retransmissions
- Improper timeout tuning
Layer 3: Network – Reachability and Routing Logic
What it looks like today
- IP addressing (IPv4 / IPv6)
- Subnets and CIDR blocks
- Routing tables
- VPCs, VPNs, peering
Why this layer matters
Layer 3 decides who can talk to whom. If routing is wrong, nothing above it works.
Modern scenarios
- Kubernetes pods resolving DNS but failing to connect due to missing cloud routes.
- Multi-cloud VPNs breaking because of overlapping IP ranges.
- Traffic unintentionally hairpinning through expensive gateways.
Performance angle
Poor routing choices increase latency and cloud egress costs. Smart IP design saves money and milliseconds.
Layer 2: Data Link – The Illusion of Locality
What it looks like today
- Ethernet frames
- MAC addresses
- VLANs
- Virtual switches
- VXLAN overlays
Why this layer matters
Layer 2 creates the illusion that machines are neighbors—even when they’re virtual, distributed, and abstracted.
Modern scenarios
- VXLAN allows Kubernetes pods on different nodes to appear on the same network.
- Virtual switches forward traffic inside hypervisors without touching physical routers.
- Misconfigured VLAN tagging silently isolates workloads.
Security insight
Layer 2 attacks like ARP spoofing still matter in virtualized environments unless explicitly mitigated.
Layer 1: Physical – The Cloud Still Runs on Hardware
What it looks like today
- Fiber cables
- NICs
- Switch ports
- Wi-Fi radios
- Data center links
Why this layer matters
No abstraction escapes physics. Latency, packet loss, and throughput ultimately depend on real hardware.
Modern scenarios
- A faulty NIC on a hypervisor impacts dozens of virtual machines.
- Oversubscribed links between racks cause random packet loss blamed on “the app.”
- Cloud providers expose Layer 1 failures indirectly via dropped packets and degraded availability zones.
Hidden danger
Physical-layer issues often produce the weirdest symptoms higher up—timeouts, retransmissions, and intermittent failures that defy logic.
Why the OSI Model Still Works in Cloud and Containerized Systems
Even though modern stacks blur boundaries, the OSI model remains powerful because it:
- Turns vague complaints into structured diagnosis
- Helps teams isolate security risks by layer
- Prevents wasted effort fixing the wrong problem
- Improves communication between DevOps, networking, and security teams
When something breaks, it breaks at a layer—whether or not the tool you’re using names it.
Final Thought
The OSI model isn’t about memorizing seven layers. It’s about thinking clearly when systems fail.
In cloud-native environments full of abstraction, the OSI model is one of the few tools that still maps cleanly to reality. If you can move confidently from Layer 7 symptoms down to Layer 1 causes, you’re not just debugging—you’re engineering.